FBI infiltrates and disrupts Hive ransomware network Cybersecurity experts warn against complacency

By Ken Showers, Managing Editor
Updated 1:46 PM CST, Fri January 27, 2023
WASHINGTON, D.C. – Diligence has paid off for the Federal Bureau of Investigations (FBI) as it revealed the results of a months-long disruption campaign against a ransomware group.
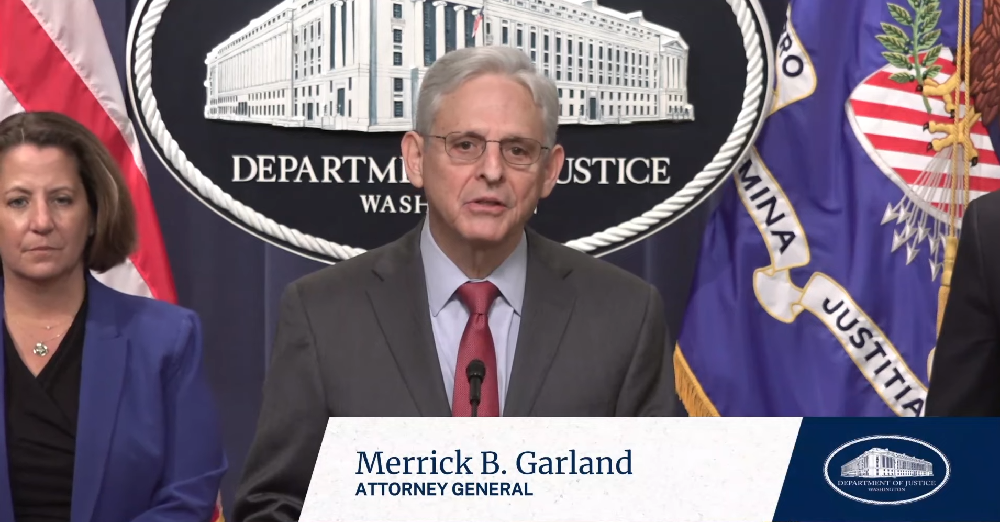
In a press conference on Jan. 26, the U.S. Department of Justice (DoJ) announced their successful penetration into the group whose targets included hospitals, school districts, and other critical infrastructure. “We are here to announce that last night, we dismantled an international ransomware network responsible for extorting and attempting to extort hundreds of millions dollars from victims in the United States and around the world,” Attorney General Merrick Garland told reporters. “Known as the Hive ransomware group, this network targeted more than 1500 victims around the world since June of 2021.”
Notable targets of the Hive include an attack on the Memorial Health System in mid-August last year, forcing hospitals to be unable to access their computers and use paper charts among other potentially deadly complications. Security Systems News reported on a similar incident that affected the CommonSpirit Health System in early October of 2022 resulting in the same issues, although it’s unclear if the attacks were related.
Thanks to the efforts of the FBI however some victims were spared as the FBI was able to provide over 300 decryption keys to victims who were under attack. In addition, the FBI were able to distribute another 1,000 keys to previous victims the DoJ stated in a press release on the campaign. They also stated that through working together with German law enforcement and the Netherlands National High Tech Crime Unit they were able to seized control of the servers and websites the Hive used to communicate with members.
“Cybercrime is a constantly evolving threat. But as I have said before, the Justice Department will spare no resource to identify and bring to justice, anyone, anywhere, who targets the United States with a ransomware attack,” Garland said. “We will continue to work both to prevent these attacks and to provide support to victims who have been targeted. And together with our international partners, we will continue to disrupt the criminal networks that deploy these attacks.”
Some security experts are warning that the threat is far from over, however. “Hive ransomware group was one of the most prolific ransomware gangs in the last five years. Hive adopted all of the recent trends in the ransomware scene and became a major player in the Ransomware-as-a-Service business,” Hüseyin Can Yuceel, a security researcher for Picus Security told SSN. “The FBI's press release did not give any specific names. There is no attached indictment. Sophisticated ransomware threat actors are not easy-to-identify, and even if they are identified, they may not be within the agency's reach. That's why the FBI took the next best approach and disrupted the group's operations. The attached warrant is for the seizure of servers used by Hive and located in California, which falls under FBI jurisdiction.”
As it stands, Yuceel cautions that the difficulty of catching the perpetrators in addition to the incredibly lucrative nature of the ransomware-as-a-business model means that the remnants of Hive will likely regroup and resume operations in the future unless strong international cooperation is met to challenge ransomware operations.
The FBI has asked that victims of Hive ransomware should contact their local FBI Field office for further information. For more details on the tactics used by the Hive ransomware group another Picus Security researcher, Sila Ozeren, goes into depth on it in a technical blog here.
Comments